A packet filtering firewall, designed to regulate incoming and outgoing packets from a network or an operating system, is akin to security personnel guarding the entrance to a commercial or residential property. Such a system has very little authority, unless given additional powers, in what applications inside the operating system or network are able to do.
That is where an application “firewall” comes into play. It is designed to ensure that applications in an operating system (or in some instances, a network) adhere to access control rules that govern their “activities.” It should be noted that an application firewall, like a stateful packet filter, is not a one-shot security solution. It merely adds an extra layer of security to a system, complementing other security protocols and systems in place. That idea also formed the main point of why your computer needs a firewall enabled.
This crude sketch shows applications in an operating system when there is no application firewall to regulated their actions. They are free to wander as they please.

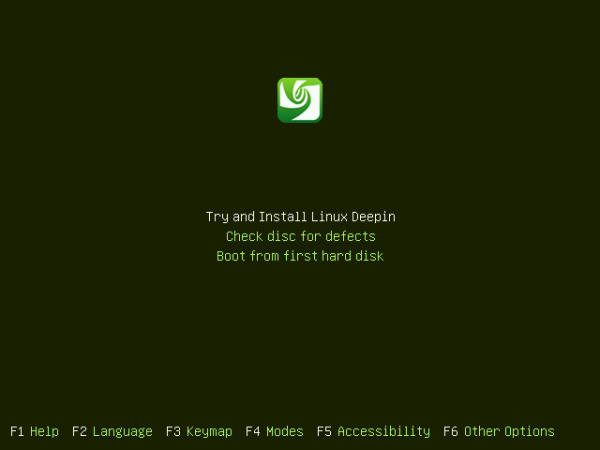
And here is what it looks like with an application firewall activated. By the way, this screen shot and the one above, were taken from Tomoyo’s website, an application firewall featured in this article:

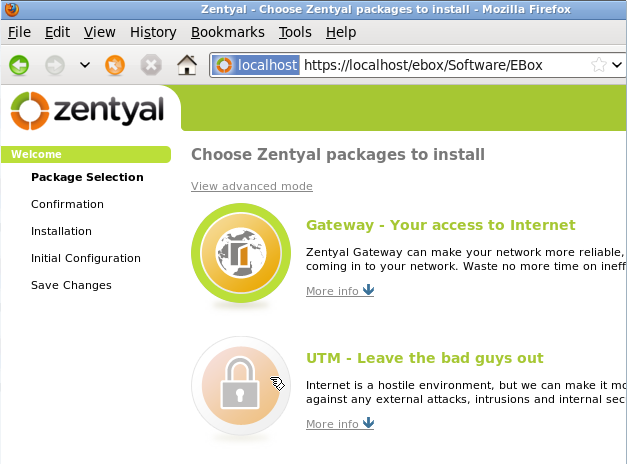
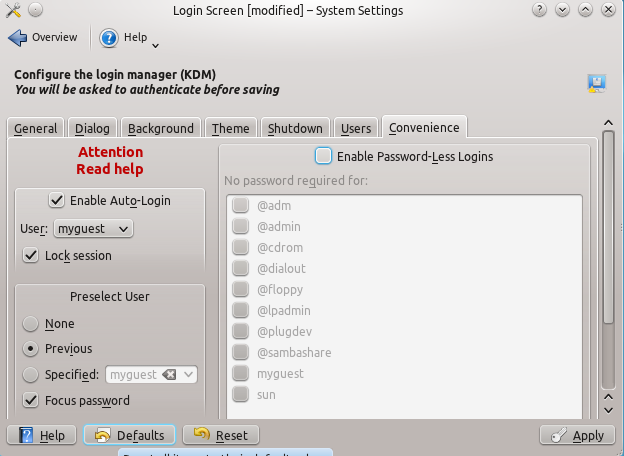
There are three such applications built into the Linux kernel, and they are available as loadable modules. While they tend to be described using slightly different terminologies, and may even differ in how to operate, once activated, they have the same effect – intelligently enforcing access rights for applications they are configured to monitor. In alphabetical order, the three application firewalls are:
AppArmor, or Application Armor, is currently maintained by Canonical, and is activated by default in Ubuntu. It is officially described as:
An effective and easy-to-use Linux application security system. AppArmor proactively protects the operating system and applications from external or internal threats, even zero-day attacks, by enforcing good behavior and preventing even unknown application flaws from being exploited. AppArmor security policies completely define what system resources individual applications can access, and with what privileges. A number of default policies are included with AppArmor, and using a combination of advanced static analysis and learning-based tools, AppArmor policies for even very complex applications can be deployed successfully in a matter of hours.
SELinux, or Security-Enhanced Linux, was contributed to the Linux kernel by the National Security Agency. It is the application firewall activated by default in Fedora, and it has a reputation as being a bit more difficult to manage and configure than the others. The following is a brief description of SELinux from its Fedora project page.
Security-Enhanced Linux (SELinux) adds Mandatory Access Control (MAC) to the Linux kernel, and is enabled by default in Fedora. A general purpose MAC architecture needs the ability to enforce an administratively-set security policy over all processes and files in the system, basing decisions on labels containing a variety of security-relevant information. When properly implemented, it enables a system to adequately defend itself and offers critical support for application security by protecting against the tampering with, and bypassing of, secured applications.
MAC provides strong separation of applications that permits the safe execution of untrustworthy applications. Its ability to limit the privileges associated with executing processes limits the scope of potential damage that can result from the exploitation of vulnerabilities in applications and system services. MAC enables information to be protected from legitimate users with limited authorization as well as from authorized users who have unwittingly executed malicious applications.
Tomoyo was launched in 2003 and its development is sponsored by Japan’s NTT DATA Corporation. It is, as far as I know, the only one that is not used by default on any Linux distribution. However, that should change when the next edition of Chakra Edn is released. According to the official description, Tomoyo is a:
Mandatory Access Control (MAC) implementation for Linux that can be used to increase the security of a system, while also being useful purely as a system analysis tool.
TOMOYO Linux focuses on the behaviour of a system. Every process is created to achieve a purpose, and like an immigration officer, TOMOYO Linux allows each process to declare behaviours and resources needed to achieve their purpose. When protection is enabled, TOMOYO Linux acts like an operation watchdog, restricting each process to only the behaviours and resources allowed by the administrator.
Most distributions have one of these applications activated by default. If yours does not, talk to the developer(s) about it. Sometimes, all you need to do is install the userland utilities for managing it.




Nice little writeup, but I agree with the other folks. This is MAC,not an application-level “firewall” (quotes or not). Check Wikipedia’s impression of what a firewall is.
Also, way too close to name collision with an application-layer firewall. (And that’s what I thought I would be reading about when I visited here.)
Since you mentioned Wikipedia, here’s a nice little quote from a Wikipedia page on “Application Firewall” (under “Host-based application firewalls”):
From the same article, comes this line: “The application firewall is typically built to control all network traffic on any OSI layer up to the application layer.”
It’s a very nice article. You may read the whole thing here.
You may ask yourself why you have to spend so much effort defending the title of an (otherwise fine) article.
These are not really Linux Firewalls, Firestarter or GUFW are….right?
These are not firewalls in the traditional sense, but they work at the application level in very much the same manner that packet filtering firewalls work. They are better known as Mandatory Access Control applications.
Firestarter or GUFW are just frontends for IPTables/Netfilter, a real packet filtering firewall.
This isn’t really a “firewall” any more than /bin/login and file permissions are. This is really more about access control on the box, i. e. once you’re already on there. That said, mandatory access control (MAC) certainly can help guard against certain types of attacks. Haven’t gotten around to AppArmor yet due to my environment, but I can confirm the general benefits from my experience with SELinux. Once I learned how to work it, I stopped turning it off and started tuning it to my systems.
But that’s why “firewall” is in quotes.
It just me or AppArmor / Application Armor not available under Debian testing ?